Is your domain being used by fraudsters to spoof your customers?
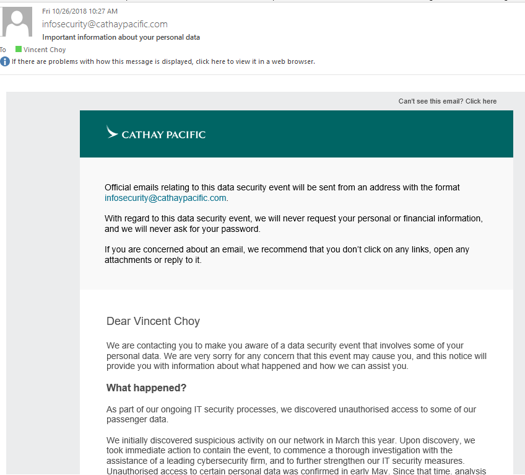
Last November, I was one of 9.4 million people to receive an email from Cathay Pacific, warning me that my data was stolen. The airline, which saw its share price take a beating due to this data breach, kindly warned me to be alert for phishing emails that attempt to scam me.
You may think you are safe because you haven't flown on Cathay Pacific, or British Airways, or done business with any of the global companies that recently reported data breaches. You are not.
None of Malaysia's top 30 listed companies, including banks and telcos, have fully set up the defences needed to prevent fraudsters from using their domains to send you phishing emails. These 30 companies are just a fraction of Malaysia's 261,000 businesses that have online presences such as corporate websites on the Internet. Indeed, the stock exchange Bursa Malaysia has not done so itself.
At least one of Malaysia’s most popular online shopping sites has also left its domain unprotected, and left a large number of Malaysia’s 15.3 million online shoppers vulnerable to receiving scam emails using its name.
These companies have not prevented the unauthorized use of their email domain to protect people from spam, fraud, and phishing.
In contrast, Monash University Malaysia, one of Malaysia’s top private universities, has done better, setting up a strict sender authentication framework. This means it is quite difficult for anyone to impersonate the university and send you a fake email from a spoofed @monash.edu.my address.
Many companies have put in place firewalls, anti-spam and anti-virus tools, and some even may encrypt their emails. These measures do give their own email users – their staff, top management and company directors — some but not always full protection.
Encryption means scrambling the contents of emails, so confidential information is not easily readable. Firewalls help prevent attacks from outside, and antivirus prevents infection by certain kinds of malware. Spam filters protect companies’ own email users from junk email as well as some phishing attempts.
Generally, these are insufficient to prevent sophisticated scammers from pretending to be these companies and using valuable brand names to attack other people through email. To get the right protection, companies need to implement the three email security standards known as SPF, DKIM, and DMARC.
If you want to check if your employer or company needs sender authentication, try the free tools on phishingscorecard.com and check whether your SPF, DKIM or DMARC settings have been set. There are many service providers including dmarcian.com, which Fedelis Sdn Bhd represents in Malaysia, that will advise companies on how to set up and maintain these security standards effectively.
Without sender authentication, it is laughably easy to impersonate them and trick the unwary public into transferring money, or revealing personal information, or revealing your bank account passwords. If this happens, these companies could see their share prices drop like Cathay Pacific did, and damage the value of their brands.
Even a mischief-maker could wreak havoc. I know of one case where a spoofed email was sent, cancelling a big company meeting as a prank. Criminals or pranksters, they could even pretend to be a federal agency like the JPJ and send you all manner of fake emails.
So what can be done to improve email security?
First, whether as an individual or a company, ensure that you are using a world class email service, such as Office365, which provides sophisticated technology to help identify and stop phishing attempts, and uses standards like SPF, DKIM and DMARC to protect you, your company and its customers.
Second, ensure your own domain is protected by SPF, DKIM and DMARC, to prevent fraudsters from using it to target your own staff, or your customers who may receive emails they think is from you. Companies must not only deploy these standards, but also ensure the settings are correct. Of the top 30 Malaysian listed companies mentioned above, none has setup sender authentication fully or properly.
It's easy to blame the victims for falling for phishing emails. But this should be shared by those companies that don't stop the phishing from happening. It's probably what caused Cathay Pacific's data breach in the first place
